At Northwoods Web Designs, we are committed to ensuring the security and reliability of our client’s websites. As part of our ongoing efforts to provide our clients with the best possible website services, we are sharing some crucial items included in our Website Care Services to enhance your website’s security.
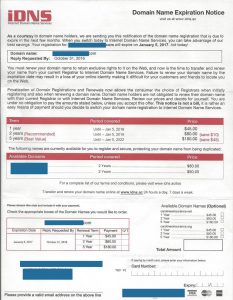
SSL Certificates: At Northwoods Web Designs, we prioritize the security of our clients’ websites. That’s why we implement Secure Sockets Layer (SSL) certificates to establish a secure connection between our clients’ websites and their visitors. By having an SSL certificate, we ensure that any sensitive data transmitted through our clients’ websites, such as personal information or credit card details, remains encrypted and protected from potential hackers.
Regular Updates: We understand the importance of keeping our clients’ websites secure. That’s why we proactively monitor and apply regular updates to our client’s website software. By keeping plugins, themes, and CMS versions up to date, we minimize the risk of potential vulnerabilities that can be exploited by attackers. You can rest assured knowing that we prioritize the security of our client’s websites by promptly checking for updates and applying them to protect against potential security breaches.
Website Backups: Our client’s peace of mind is our priority. That’s why we regularly back up our clients’ websites to ensure their security and reliability. In the event of a security breach or website malfunction, our recent backups allow us to quickly restore our clients’ websites to their previous state with minimal data loss or downtime. With our reliable backup system in place, our clients can focus on their business while we handle the security of their websites.
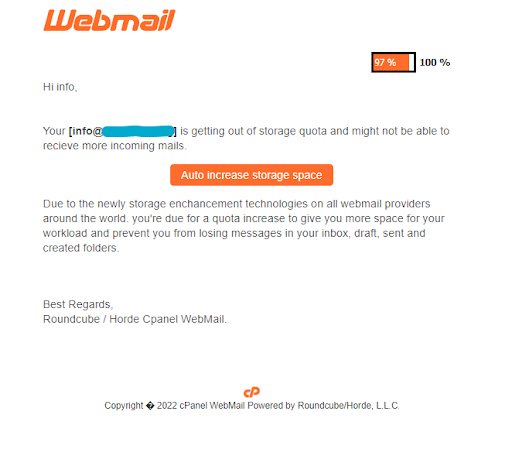
Spam and Malware Prevention: We take proactive measures to protect our clients’ websites from spam and malware. Our team deploys effective spam filtering and malware scanning techniques at both the server and website levels. By regularly scanning and cleaning our clients’ websites, we minimize the risk of potential security vulnerabilities and keep their websites running smoothly and securely.
Regular Security Audits: At Northwoods Web Designs, we are committed to providing our clients with the highest level of security. That’s why we conduct regular security audits and vulnerability assessments for our clients’ websites. By proactively identifying potential loopholes or weaknesses in our clients’ website security infrastructure, we can swiftly patch any vulnerabilities and keep their websites secure. Additionally, our penetration testing allows us to simulate real-world attacks to ensure that our client’s websites are protected against potential threats.
Requiring Strong Passwords: One of the simplest yet most effective ways to protect your website is by using strong passwords. We require strong passwords when accessing our technologies such as our Client Billing Area, or the Website Portal Dashboard where website edits are completed by our clients. We require using a combination of uppercase and lowercase letters, numbers, and special characters.
With Northwoods Web Designs, you can trust that we prioritize our client’s website’s security and take the necessary measures to benefit their online presence.
Interested in our Web Care Services Plans? We currently have availability and would love to welcome you to join our family at Northwoods Web Designs. With our top-notch website maintenance and hosting services, you can rest assured that your website will be secure, optimized, and running smoothly. Join our community of satisfied clients and experience the peace of mind that comes with knowing your online presence is in capable hands. Don’t miss this opportunity to elevate your website’s performance and security. Contact us today and become a valued member of the Northwoods Web Designs family.